What is Cyber Threat Intelligence? A Simplified Guide for 2025
Discover how cyber threat intelligence can transform your security strategy and keep your organization safe from evolving threats
Cyber threat intelligence (CTI) is a vital component of modern cybersecurity strategies that involves collecting, analyzing, and disseminating information about potential or current threats to an organization’s digital assets. The CTI analysis process aims to provide actionable insights that help organizations anticipate, identify, and mitigate cyber threats before they can cause significant harm.
With cyberattacks becoming more frequent, costly, and sophisticated and attack methods evolving rapidly, organizations need all the insights they can get to defend against these ever-changing threats. Every day, organizations face the challenge of quickly answering critical questions like:
- Are there any new types of attacks?
- Are our devices susceptible to these threats?
- Has an important new vulnerability been discovered in a trusted piece of software?
- Have certain threat groups begun targeting organizations in our industry?
Cyber threat intelligence is the secret weapon that helps security operations center (SOC) teams and other stakeholders confidently tackle tough questions and fend off future attacks. By harnessing real-time threat data and advanced analytics, CTI empowers organizations to stay one step ahead of cybercriminals.
But what exactly goes into crafting a CTI strategy? And how can leveraging CTI transform an organization?
In this post, we’ll provide an in-depth definition of cybersecurity threat intelligence, compare the different types of threat intelligence, and analyze its importance in helping organizations achieve better security. We’ll also present a deeper explanation of how the CTI process works by considering the typical lifecycle from data collection and threat analysis to sharing this intelligence. We’ll then illustrate what the core components of the CTI lifecycle look like using an everyday scenario to help simplify this explanation further.
Finally, we’ll look at how you can integrate cyber threat intel into your current tools and operations and the key features to look for in a solution that supports effectively leveraging threat intelligence to proactively defend against developing risks.
- What is threat intelligence in cybersecurity?
- What are the different types of threat intelligence?
- Why is using cyber threat intelligence important?
- How does the threat intelligence lifecycle work?
- Real-world CTI lifecycle example: Home security
- How to implement cyber threat intelligence into your security strategy
- Choosing a comprehensive threat intelligence solution
- Benefits of integrating threat intelligence with SIEM and AEM
- Improving threat intelligence with autonomous endpoint management
What is threat intelligence in cybersecurity?
Cybersecurity threat intelligence involves collecting, analyzing, and disseminating data to help organizations understand the threats that can compromise their systems, networks, and assets.
By gathering information from various sources like open-source intelligence (OSINT), indicators of compromise (IOCs), and threat feeds, CTI helps organizations understand the tactics, techniques, and procedures (TTPs) used by threat actors to identify patterns and trends in cyber threats, which organizations can use to enhance their threat detection capabilities to protect critical resources and information. Not only does this improve incident response, but it also helps allocate security resources and prioritize efforts to address the most pressing threats.
To effectively manage these processes, organizations commonly implement a threat intelligence program, which includes the people, workflows, and tools needed to handle all phases of the threat intelligence lifecycle. The goal is to ensure that insights about new cybersecurity threats are delivered to SOC teams, security professionals, and other key stakeholders in a timely and helpful manner, enabling informed decisions and effective security measures.
Imagine having a system that not only detects threats but also helps you understand the bigger picture. With CTI, you can stay ahead of cyber threats, allocate resources wisely, and ensure your team is always prepared.
Now that we have a clearer understanding of what threat intelligence in cybersecurity entails, let’s dive into how different types of threat intelligence provide unique insights that help organizations create more robust and proactive security strategies.
First, we’ll explore the three main types of threat intelligence to discover how each plays a crucial role in safeguarding against cyber threats. Then, we’ll examine a potential fourth type of threat intelligence that’s emerging in the cybersecurity landscape.
What are the different types of threat intelligence?
Since each stakeholder requires specific information to protect the organization from cyber threats effectively, there are also different types of threat intelligence.
Think of threat intelligence like a tailored suit—one size doesn’t fit all. For example, tactical threat intelligence, which includes details like IP addresses and TTPs, might not be very useful to boards of directors. However, strategic threat intelligence, which provides insights into new threat actors and industry trends in cyberattacks, is exactly what they need to make informed decisions.
On the other hand, operational threat intelligence is like the daily weather forecast for your security team. It provides real-time information about specific threats that are actively targeting your organization. For instance, if there’s an ongoing phishing campaign targeting your industry, operational threat intelligence will alert your security team so they can take immediate action to mitigate the threat.
Just like you wouldn’t give an executive the same type of reporting you would provide a security professional, different types of threat intelligence should be used by different key stakeholders for different purposes. Still, all types of threat intelligence are essential to an organization’s mission to prevent and mitigate threats in real time.
Building from these examples, we can categorize threat intelligence information into three types of distinct information:
- Strategic threat intelligence provides executive-level security professionals with a high-level view of an organization’s threat landscape. This information is essential for making informed decisions about cybersecurity investments, hiring, and company-wide security initiatives, such as mandating security training for all employees to guard against potential attacks.
[Read also: 4 critical leadership priorities for CISOs in the AI era]
Strategic threat intelligence encompasses insights into known vulnerabilities, attack trends, and threat actors’ motivations, capabilities, and recent activities. This information is tailored to the organization’s specific IT environments and business models, helping leaders understand potential risks and prioritize their security efforts accordingly.
This level of CTI often includes intelligence reports and whitepapers from analysts and security firms, offering a comprehensive understanding of the threat landscape. By leveraging these insights, leaders can ensure a proactive and robust cybersecurity posture, safeguarding their organizations from cyber threats. - Operational threat intelligence falls between strategic and tactical intelligence in terms of specificity. It focuses on the tactics, techniques, and procedures threat actors use to help organizations understand and respond to ongoing threats. It also involves the real-time monitoring and analysis of network and endpoint activity to detect device vulnerabilities, indicators of compromise, and emerging threats. This type of intelligence provides security operations center teams and other security professionals with continuous, up-to-date information about the status and behavior of networks and endpoints.
Using this intelligence data, organizations can anticipate attack vectors and implement proactive measures to defend against them. This type of intelligence provides a more comprehensive view of the threat landscape, enabling organizations to gauge risk, oversee remediation methods, and ensure that IT assets are protected against new attack vectors and threats identified in threat intelligence feeds.
Operational threat intelligence is essential for maintaining a proactive security posture. It enables security teams to gain insights into the broader threat patterns used by and behavior of threat actors, allowing them to understand the origin, intent, and complexity of the threats they face. - Tactical threat intelligence offers in-depth technical threat data, including IOCs like IP addresses, file hashes, and malware signatures, to security professionals. This type of intelligence is crucial for enabling quick and effective detection and mitigation of threats, which proactive efforts like threat hunting depend on.
Tactical threat intelligence also includes more detailed information about the TTPs threat actors use. By understanding these TTPs, security teams can anticipate the methods attackers might use and implement appropriate defenses. This level of intelligence is often derived from real-time monitoring and analysis of network traffic, endpoint activity, and threat intelligence feeds.
By providing actionable insights, tactical threat intelligence helps teams respond swiftly to emerging threats, ensuring they can protect the organization’s assets and data in real time. It also supports the development of detection rules, such as YARA (an open-source tool for malware detection and classification), and crafting signatures for intrusion detection systems (IDS) and intrusion prevention systems (IPS). Additionally, it aids in formulating security information and event management (SIEM) correlation rules, all of which enhance the detection of malicious activities.
Free eBook: How to build a mature threat hunting program
It’s important to note that with the landscape of threat intelligence continually evolving, some experts argue that an additional fourth type of threat intelligence warrants recognition.
In the next section, we’ll explore this perspective, examining the rationale behind the inclusion of a fourth type and how it further enhances the overall threat intelligence framework.
Are there three or four types of threat intelligence?
Some security experts recognize a fourth category of threat intelligence called technical threat intelligence. However, it is debated whether technical threat intelligence should be classified separately or remain a subset under the broader category of tactical threat intelligence due to its detailed and technical nature.
Like tactical threat intelligence, technical threat intelligence provides detailed technical information about specific attacks and exploits in a manner that makes the intel more immediate and actionable. For example, tactical threat intelligence can include detailed descriptions of attack vectors, techniques, and specific vulnerabilities attackers exploit.
Who decides whether there are three or four types of cyber threat intelligence? You do. How many types of threat intelligence you decide to use is dependent on whether you choose to incorporate actioning insights into the methods and strategies used by attackers as part of your technical threat intelligence strategy or address them through separate tactical threat intelligence activities can vary depending on your organization’s context and specific needs.
For some organizations, incorporating these insights directly into their tactical threat intelligence framework can streamline the process of identifying and mitigating threats. This approach allows for a cohesive strategy where detailed technical data is analyzed alongside the TTPs used by attackers. By doing so, organizations can enhance the overall effectiveness of their threat intelligence program, providing a comprehensive view of the threat landscape.
On the other hand, some organizations may find it more beneficial to handle these insights through distinct technical threat intelligence activities. This approach can allow them to focus on the immediate and actionable aspects of threat intelligence, enabling a more targeted response to specific threats. It can be particularly useful for organizations with dedicated security teams specializing in real-time threat detection and response.
Ultimately, deciding how to incorporate these threat intelligence insights will depend on various factors, including the organization’s size, resources, threat landscape, and cybersecurity strategy. By carefully considering these factors, organizations can determine the most effective way to leverage both technical and tactical threat intelligence to enhance their cybersecurity posture and protect against evolving threats.
However, understanding the types of threat intelligence is just the beginning. The real question is, why is using cyber threat intelligence so essential for organizations today? In the next section, we’ll discuss the importance of cyber threat intelligence and how it plays a vital role in securing essential assets and sensitive data.
Why is using cyber threat intelligence important?
Cyber threat intelligence is crucial to effective cybersecurity because it uniquely focuses on understanding the human element driving cyberattacks. This deeper insight helps develop robust defense strategies that are more effective in countering threats.
Human behavior remains one of the most unpredictable factors in cybersecurity. CTI has created a streamlined process to achieve this easily, making it a differentiator for more effective cybersecurity.
With CTI, it’s not just about the data; it’s about understanding the people behind the threats and staying one step ahead. Unlike traditional security methods, CTI helps organizations understand the motivations and methods of threat actors, providing actionable insights beyond mere data collection.
By continuously leveraging the latest threat intelligence, news reports, and industry research, CTI compiles a comprehensive understanding of the threat landscape. This process distills meaningful, actionable insights by transforming raw data to address an organization’s specific risk profile, making it easier to focus on what truly matters. As a result, organizations can better anticipate and proactively counteract cyber threats, ensuring the security of devices and the business critical assets they contain.
[Read also: How AI enhances anomaly detection and eases alert fatigue]
This holistic approach not only enhances threat detection and incident response but also fosters collaboration and intelligence sharing, which leads to the development of more effective cybersecurity measures across the industry, making CTI an indispensable tool in improving modern security strategies for all.
Organizations can stay ahead of cyber threats and ensure their assets and data are well-protected by embracing the CTI process. This comprehensive approach not only enhances threat detection capabilities but also improves incident response and resource allocation, making it a necessary component of modern cybersecurity strategies.
Now that you understand why using CTI is important, let’s look at how this type of intelligence is collected, analyzed, and delivered.
How does the threat intelligence lifecycle work?
The threat intelligence lifecycle is a structured process used in cybersecurity to manage and respond to cyber threats effectively. It involves several phases that convert raw data into actionable intelligence through planning, collecting, analyzing, compiling, and disseminating the information in an actionable way.
Let’s review a step-by-step outline of the five phases in a threat intelligence lifecycle:
- Planning: The CTI lifecycle begins with setting the direction and aligning on objectives for the CTI program. Activities include defining goals, determining the threat types to focus on, and identifying the resources needed to ensure that efforts align with the overall security strategy.
- Collecting: After planning, the next phase involves data collection from various sources to collect as much relevant information about potential threats, including:
- Analysis: Once collected, this raw data undergoes thorough analysis to identify patterns, trends, and potential threats to understand threat actors’ tactics, techniques, and procedures better.
Framing threat intelligence in terms of TTPs helps turn complex and varied data sets into actionable threat intelligence that security teams can apply quickly and effectively to stop threats by gaining insights into the behavior and methods used by threat actors, allowing teams to anticipate and mitigate potential attacks. - Production: Once collected and analyzed, the processed data is transformed into actionable intelligence. This involves evaluating the relevance and impact of the information, ensuring it meets the organization’s requirements, and preparing it for dissemination to key stakeholders.
- Dissemination: The final step involves distributing the collected data and analysis to relevant stakeholders. Threat intelligence data is sent to security control tools, such as threat detection systems and threat monitoring dashboards in the SOC.
Security professionals and automated tools then use this data to enhance threat detection, hunting, and remediation. This phase ensures that decision makers, security staff, and other teams receive the information promptly and securely, enabling them to take appropriate actions based on the intelligence.
• External threat feeds: Information sourced cyber threat activity taking place around the world
• Internal logs: Telemetry data collected from within the organization’s systems
• Honeypots: Decoy systems set up to attract and monitor cyber attackers
• Human intelligence, or HUMINT: Insights from discussions on hacker forums, activity on the dark web, and social media
• Open-source intelligence, or OSINT: Information about known vulnerabilities, threat actors, attack methods, and indicators of compromise
While this description of the CTI lifecycle helps illustrate how each phase contributes to a comprehensive security plan, only having the purely theoretical explanation fails to capture the full picture.
In the next section, we’ll explore how these steps can be adapted to home security, providing a clear and practical illustration of the lifecycle in action.
Real-world CTI lifecycle example: Home security
To better understand the cyber threat intelligence lifecycle, let’s consider how you might use the same steps to protect the security of your home.
-
Planning your security system
Just like you would plan which areas of your home need protection (doors, windows, etc.), using insights from cyber threat intelligence, you can identify what needs to be protected and the potential threats. - Collecting the evidence
Next, you gather information about potential threats by installing security cameras, motion sensors, and alarms. With threat intelligence, you collect data from various sources, such as networks, devices, and threat data feeds.
You also might pay attention to alerts from police and other authorities who regularly issue reports about trends in criminal activity. Similarly, organizations would pay attention to official reports about cybercrime from sources like the FBI and the Cybersecurity & Infrastructure Security Agency (CISA). - Analyzing the footage
You review the footage and alerts from your security system to filter out false alarms and focus on real threats. Threat intelligence is like this security footage and allows analysts to examine the processed data to understand the tactics and techniques used by cyber threats.
You can also look for false positives (alerts that seem suspicious but turn out not to be) and train your security systems to ignore those types of alerts automatically, just like a SOC team would filter out alert noise so it can pay more attention to the issues that matter. - Producing the learnings
You identify from the security footage and other sources if there is any suspicious activities or patterns, like someone lurking around your house. Similarly, with threat intelligence, you process the collected data to make it usable for determining next steps.
During this step, you can gather feedback from your family or neighbors to improve your home security measures, just as you would collect feedback to refine and enhance the threat intelligence process. - Disseminating the information
You share the information about potential threats with your family or neighbors, so they know what to look for. In cyber threat intelligence, the analyzed intelligence is shared with relevant stakeholders in an actionable format.
As you would proactively protect your home, following the threat intelligence lifecycle can help organizations proactively identify and mitigate security threats, ensuring their sensitive information remains secure.
Using the CTI lifecycle steps, we can see how each phase contributes to creating a comprehensive security plan. This relatable example helps illustrate the real-world application of threat intelligence and its importance in safeguarding your digital assets.
Now, let’s shift our focus to the broader context of cybersecurity. In the next section, we’ll provide an overview of best practices for implementing cyber threat intelligence into a security strategy, ensuring organizations can effectively leverage CTI to defend crucial assets and confidential information.
How to implement cyber threat intelligence into your security strategy
Integrating cyber threat intelligence into your security strategy is essential for staying ahead of evolving threats and protecting your organization’s assets and data.
Whether you are just starting to build your threat intelligence program or looking to refine your existing strategy, here are some key steps and best practices to help you effectively incorporate cyber threat intelligence into your security framework:
- Define your goals: The first step in integrating cyber threat intelligence is clearly defining your objectives. Understanding what you aim to achieve with threat intelligence will guide your entire strategy. Are you looking to enhance threat detection, improve incident response, or gain insights into potential threats?
Whether it’s blocking malicious IP addresses, understanding threat actor motivations, or gaining historical insights, defining your goals will help you determine the type of intelligence you need and how to use it effectively.
It’s also important to ask various stakeholders about their needs for CTI and incorporate those requirements into your plan. Engaging with stakeholders, such as IT, security teams, and other business units, ensures that the threat intelligence strategy aligns with the organization’s overall goals and addresses specific needs. This collaborative approach helps identify the most relevant threats, prioritize resources, and ensure the intelligence gathered is actionable and beneficial for all parties involved. - Select relevant intel sources: Choosing the right sources for your threat intelligence involves selecting relevant and reliable external sources that provide actionable insights tailored to your organization’s needs and industry. These sources should come from a variety of channels, including organizational, community, and third-party intelligence. Doing so ensures that the data you receive is applicable and actionable, complements your internal data, and helps identify emerging threats that may not yet be visible within your organization.
Additionally, it is vital to regularly revisit whether your current threat intelligence sources provide your business leaders, IT leaders, and security teams with all the necessary data to ensure your security measures remain effective and up to date. This data should help them understand risks, implement effective security controls, stay informed about breaking news related to cyber threats, and quickly detect and mitigate threats. Given the constantly evolving threat landscape, this should be an ongoing task. - Centralize your systems: Integrating your various security systems with the threat intelligence system can ensure that insights from intelligence feeds and other sources of cyber threat intelligence can be instantly shared with security teams and security systems, where they can be used.
The more tightly integrated threat intelligence is with other security tools, the more effective your cyber threat intelligence efforts can be. For example, real-time device information collected from devices across the organization and aggregated by an endpoint management solution can inform other critical systems, such as SIEM solutions, firewalls, and other cybersecurity tools, for a more coordinated and efficient response to threats. - Determine actionable intelligence: Identifying and prioritizing relevant intelligence is essential for effective threat management. By considering how a particular threat could affect your organization and factors such as your industry, the technologies you use, and your existing security posture, you can better contextualize the intelligence you receive to make informed decisions about which threats to prioritize.
This step must involve filtering out noise and focusing on intelligence pertinent to your organization. To achieve this, implement mechanisms to filter out irrelevant data and prioritize intelligence directly impacting your organization. This can involve automated tools that sift through large volumes of data to highlight pertinent threats and processes where analysts review and validate the intelligence. - Streamline actioning insights: The final step is to act on the intelligence gathered. You can start by developing detailed response playbooks that outline specific actions to take when certain types of threats are identified. These playbooks should be regularly updated to reflect the latest threat intelligence and best practices.
To ensure quick and reliable security efforts, modern organizations are embracing opportunities to automate processes where possible for immediate protection and continuous defense against threats. For example, you can implement automation to handle repetitive and time-sensitive tasks, such as blocking malicious IP addresses, updating firewall rules, and deploying patches. Prioritizing IT automation ensures that responses are swift and consistent, reducing the window of opportunity for attackers.
To truly get value out of a comprehensive CTI program, CISOs need to lay the foundation with a solid risk management program and the infrastructure needed to appropriately analyze and contextualize the feeds they ingest.1
The current era is marked by large-scale intelligent attacks, ransomware, sophisticated malware, advanced supply chain attacks, and unknown threats. This generation [of attacks] necessitates an integrated security infrastructure, real-time threat information sharing, and the ability to defend against unknown threats. Threat intelligence plays a crucial role in this defense strategy.2
Above all else, the best guidance for how to effectively integrate CTI into a security strategy is that these efforts are never finished. Threat landscapes are dynamic, and what is relevant today might not be tomorrow.Finally, once you have these pieces in place, put your intelligence to use, see what your controls trigger on and make adjustments accordingly. Calibration is an ongoing effort—never finished, yet constantly improving.3
It’s essential to monitor and evaluate the success of your CTI strategy by regularly revisiting whether intelligence sources continue to provide actionable insights and automation efforts remain aligned with your evolving security needs by asking:
- Are teams getting the insights they need to defend against new threats? Determine if feeds and other threat intelligence sources can be broadened or fine-tuned to ensure teams get the real-time insights they need.
- Is collaboration improving across relevant teams, including IT, security, risk management, incident response, SecOps, and business stakeholders? This collaboration is crucial for sharing insights and coordinating actions, leading to a more effective and comprehensive defense strategy.
- Do teams have access to the necessary training and resources to understand and utilize the latest threat intelligence effectively? It’s essential to ensure teams understand the available threat intelligence and how it can be leveraged in their daily work.
- Are automated responses and playbooks still effective? To keep everything running smoothly, it’s important to check whether the outcomes of automation workflows are performing as expected and refining based on the latest threat intelligence and changes in your IT environment.
Having explored the best practices for implementing cyber threat intelligence into a security strategy, we can better understand how CTI enhances an organization’s security posture. But following these best practices is just the beginning.
To truly leverage the power of CTI, it’s essential to have the right solution that supports these efforts effectively. In the next section, we’ll delve deeper into the process of constructing a robust CTI solution, examining the key components and strategies that ensure successful integration and operation.
Choosing a comprehensive threat intelligence solution
Integrating cyber threat intelligence into your workstreams can be achieved through various tools, most commonly threat intelligence platforms (TIPs), SIEM systems, and autonomous endpoint management (AEM) solutions. However, these tools are not exclusive of one another. Often, the most informed threat intelligence strategies depend on leveraging components from multiple solutions.
Each solution offers unique capabilities essential to crafting a comprehensive security strategy: TIPs provide the right intelligence data, SIEM systems ensure that your security efforts are strategically informed, and AEM solutions are the driving force that enables real-time action. By integrating these solutions, you can create a robust and cohesive approach to threat detection and response, enhancing your organization’s overall security posture.
Microsoft tracks 65 trillion security signals every day to discover new and emerging threats across the global threat landscape. These data signals are just one piece of the larger CTI puzzle customers need to sift through to discover the ultimate threat… When thinking of analyzing not 1 but a 120 zettabytes is an overwhelming amount of data for human operators to try to consume and analyze to generate a high fidelity signal of CTI. Organizations need a better way to connect these disparate signals to achieve a state of comprehensive, real-time threat intelligence.4
Let’s take a closer look at how these solutions, when used together, can help organizations create a more comprehensive and robust approach to threat detection and response by allowing for better coordination among security teams, more efficient resource use, and proactive defense against evolving cyber threats.
Benefits of integrating threat intelligence with SIEM and AEM
TIPs create a consolidated view of threat intelligence from various sources, including up-to-the-minute actor, malware, and vulnerability tracking. These insights are crucial for enhancing the overall security posture of an organization. By integrating threat intelligence into various security solutions, organizations can benefit from a more comprehensive understanding of the threat landscape, enabling them to anticipate and mitigate potential risks before they materialize.
Key to actioning these insights are systems like SIEM and AEM, which play pivotal roles in supporting and actioning threat intelligence.
For SIEM solutions, the integration of external, organizational, and community-generated intelligence from TIPs allows for the aggregation and analysis of log and event data from various sources. Threat intelligence provides actionable insights into potential security events, which enables security teams to detect and respond to threats more efficiently by prioritizing alerts based on the severity and relevance of the threats. The enriched data from TIPs also helps reduce noise by allowing SIEM systems to focus on the most critical incidents, enhancing the overall security posture of the organization.
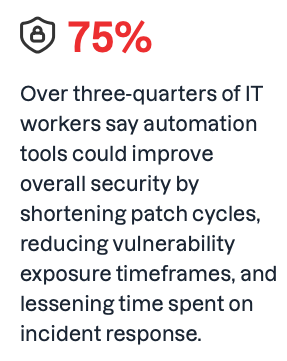
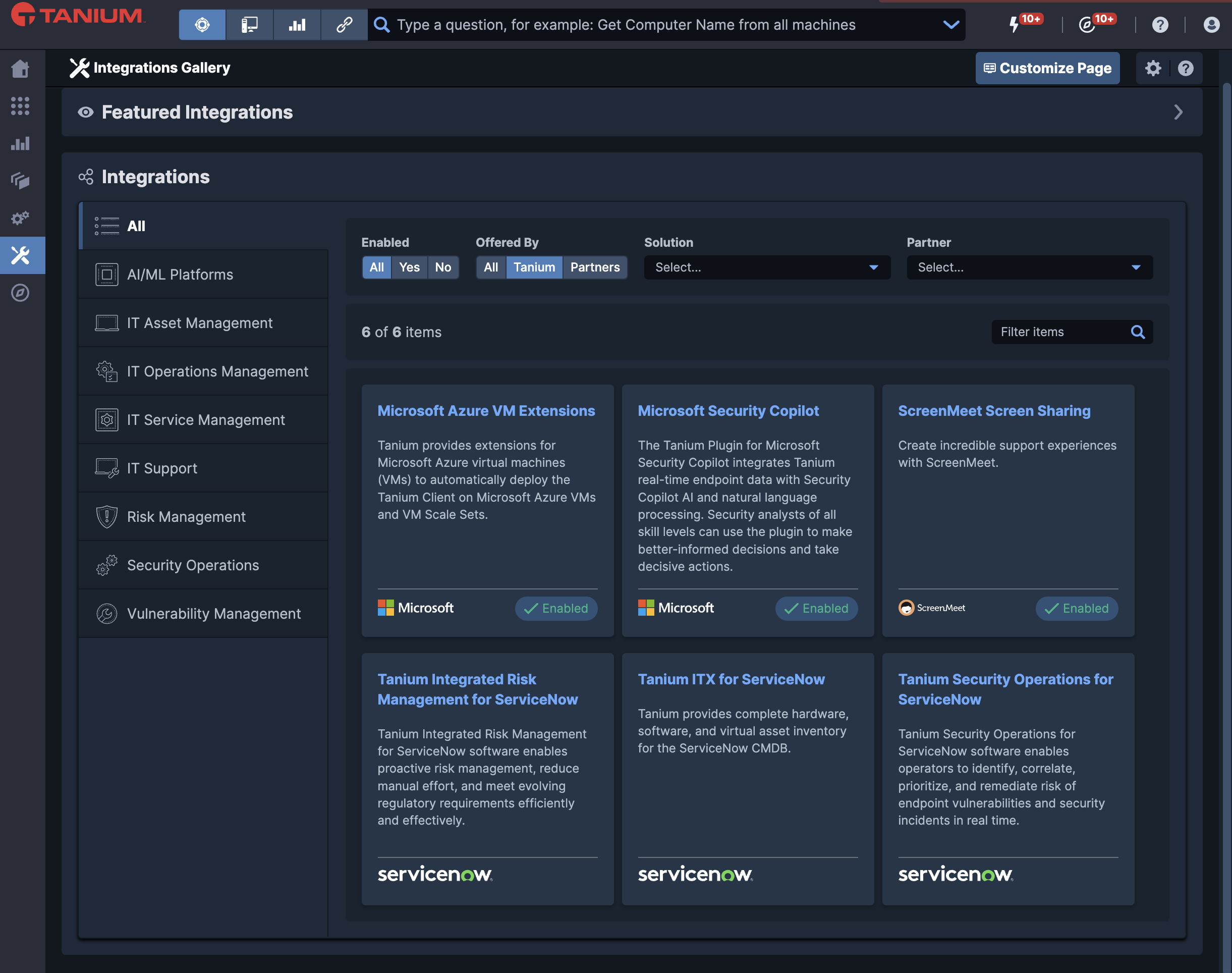
Statistic from the Tanium report, “How automation reduces burnout, improves morale, and mitigates risk,” which surveyed 110 IT professionals from companies with over 1,000 employees in Australia to uncover the impact of automation on IT teams
This helps organizations stay ahead of emerging threats by quickly identifying and mitigating potential risks outlined in the latest threat intelligence while proactively reducing the likelihood of costly breaches, minimizing the impact of cyberattacks, and maximizing the value of security investments by ensuring that resources are used efficiently and effectively.
Additionally, the real-time endpoint data and insights from AEM solutions also informs and improves SIEM systems by providing a more comprehensive view of the security landscape.
Leveraging detailed endpoint information from AEM solutions allows SIEM systems to improve threat detection and incident response capabilities, ensuring a more robust and coordinated defense against evolving threats.
[Read also: Do you trust the data in your configuration management database (CMDB)?]
By providing real-time endpoint visibility and control, AEM solutions serve as the underlying thread that weaves together the fabric of an organization’s security strategy. AEM solutions not only make threat intelligence actionable but are foundational to enhancing the overall effectiveness of security measures across your most critical systems.
In the following section, we’ll explore the various ways in which AEM solutions drive focused security automation efforts, ensuring a robust defense against emerging threats and solidifying their position as an indispensable component of modern cybersecurity.
Improving threat intelligence with autonomous endpoint management
Autonomous endpoint management leverages advanced analytics, artificial intelligence, and machine learning to enhance data analysis and threat detection accuracy and speed. By consistently managing and quickly identifying patterns in large datasets, AEM significantly enhances the speed, efficiency, and accuracy of threat detection and response to ensure no threats are missed. It also reduces human error and frees teams to focus on more strategic activities by handling repetitive tasks automatically, which, in turn, allows organizations to more easily maintain robust cybersecurity controls as they grow without being overwhelmed by manual processes.
Learn more about what AEM is with this Gartner Innovation Insight report
AEM enables many layers of automation crucial for actioning real-time threat intelligence, including immediate alerts and responses that minimize the impact of cyberattacks and allow teams to isolate and mitigate threats in real time.
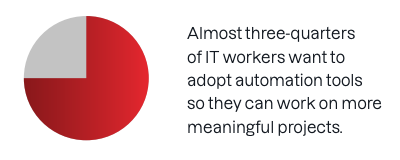
Statistic from the Tanium report, “How automation reduces burnout, improves morale, and mitigates risk,” which surveyed 110 IT professionals from companies with over 1,000 employees in Australia to uncover the impact of automation on IT teams
Additionally, AEM’s scalability ensures that it can handle increasing amounts of data and security demands, while its seamless integration capabilities with other security tools support a more comprehensive and coordinated defense against cyber threats by delivering a single source of truth to enable better team collaboration.
Integrating autonomous endpoint management into your cybersecurity strategy not only enhances threat detection and response but also significantly improves the effectiveness of threat intelligence. AEM empowers teams to quickly identify and prioritize threats based on an organization’s risk profile, ensuring that the most critical threats are addressed first. This proactive approach to integrating advanced threat intelligence capabilities ensures that valuable assets and data are safeguarded in an increasingly complex threat landscape.
As cyber threats continue to evolve, the ability to respond swiftly and effectively will be essential for maintaining business continuity and operational stability. By embracing AEM, organizations are not only enhancing their current cybersecurity measures but also preparing for the future.
Threat intelligence can become even faster and more effective when powered by AI. The Tanium platform has evolved to take advantage of real-time cloud intelligence to deliver Tanium Autonomous Endpoint Management (AEM), an advanced endpoint solution leveraging real-time data and AI insights to streamline endpoint management tasks and bolster endpoint security through intelligent automation, early detection, and rapid incident response.
Supporting both cyber threat intelligence and threat hunting in a single solution, Tanium provides the detailed, real-time, and historical data needed to assess an incident and bring endpoints back to a compliant and secure state. By augmenting threat intelligence from EDR and SIEM vendors, including our Microsoft Sentinel and ServiceNow integrations, with organizational, community, and third-party threat intelligence, Tanium combines endpoint data with broader threat intelligence efforts to help organizations better understand their threat landscape and improve their ability to detect and mitigate external and internal threats early and at scale.
Compared to traditional disjointed and manual approaches to endpoint management, AEM empowers IT and SecOps teams to make faster, more confident decisions about cyber threats and defenses. This leads to a significantly stronger security posture that effectively guards against attacks ranging from advanced persistent threats to ransomware by reducing attack surfaces while also supporting critical efforts like regulatory compliance.
Request a demo of Tanium personalized to your environment and business challenges today.